Your Data Leaked. Now What?
Do you know what to do when your information is part of a data leak?
No matter how careful you are, your data can still be leaked and your data compromised.
Careful people are still vulnerable to data leaks. A business that my health care provider uses suffered a cyber attack and a notice I received from them said that my “personal information may have been leaked.” It’s hard to know who you can trust with your information when your own healthcare provider is vulnerable, but it’s the risk that comes with giving your information to anyone.
(A promising startup called Cloaked is working on this by developing a password manager and generator as well as a telephone and e-mail address generator. The numbers and addresses work and messages get forwarded to your personal accounts, which were never in danger. In this situation, all of the contact information would have been generated from Cloaked and when the leak happens I would simply end the Cloaks through the Cloaked dashboard and cut off my tie to that information. This could be a solution for contact information but it’s not something that would keep your biometric or health data safe.)
It’s important to realize that crimes that happen with the use of your information are going to happen over time, but time is not on your side. Data breaches are not detected immediately and by the time you’ve read your notice that data has been available to criminals for weeks; when my notice was postmarked it had been seventy-three days since the data leak. Don’t assume you’re in the clear if your identity hasn’t been stolen… criminals are just waiting to get to your name on the list.
The most powerful step you can take is quick action.
So, what do you do after your data is leaked?
1. You probably received a notification, like I did, that your data was leaked (don’t thank them, they’re required by law to do so).
Hold on to the notice and take all recommendations and offers seriously.
With this in mind, hold on to any unusual mail or emails, including IRS tax notices, and bills or statements from weird sources.
2. The notice may include some attempt at compensation on the part of the company in the way of a free year of credit monitoring or identity theft monitoring. Take it and sign up right away.
3. Find out what information is out there using haveIbeenpwned.com. This site can show you if your email or phone number was in a data breach. If you have an email associated with a data breach make sure to update the password to that account immediately and/or stop using it—more on that in the next section*.
4. Update account security, especially the one compromised. Now that criminals have the personal information from your compromised account the passwords for your other accounts may now be at stake. It is surprisingly simple for hackers to guess passwords with even the smallest personal information. *A simple way to use strong passwords is to use a password manager (check out Cloaked or Bitwarden). Passwords can be automatically generated and saved for new accounts and updated easily.
Your information leaking may not have immediate repercussions, but don’t let that keep you from making sure your personal information is safe.
Cyberattacks Happen
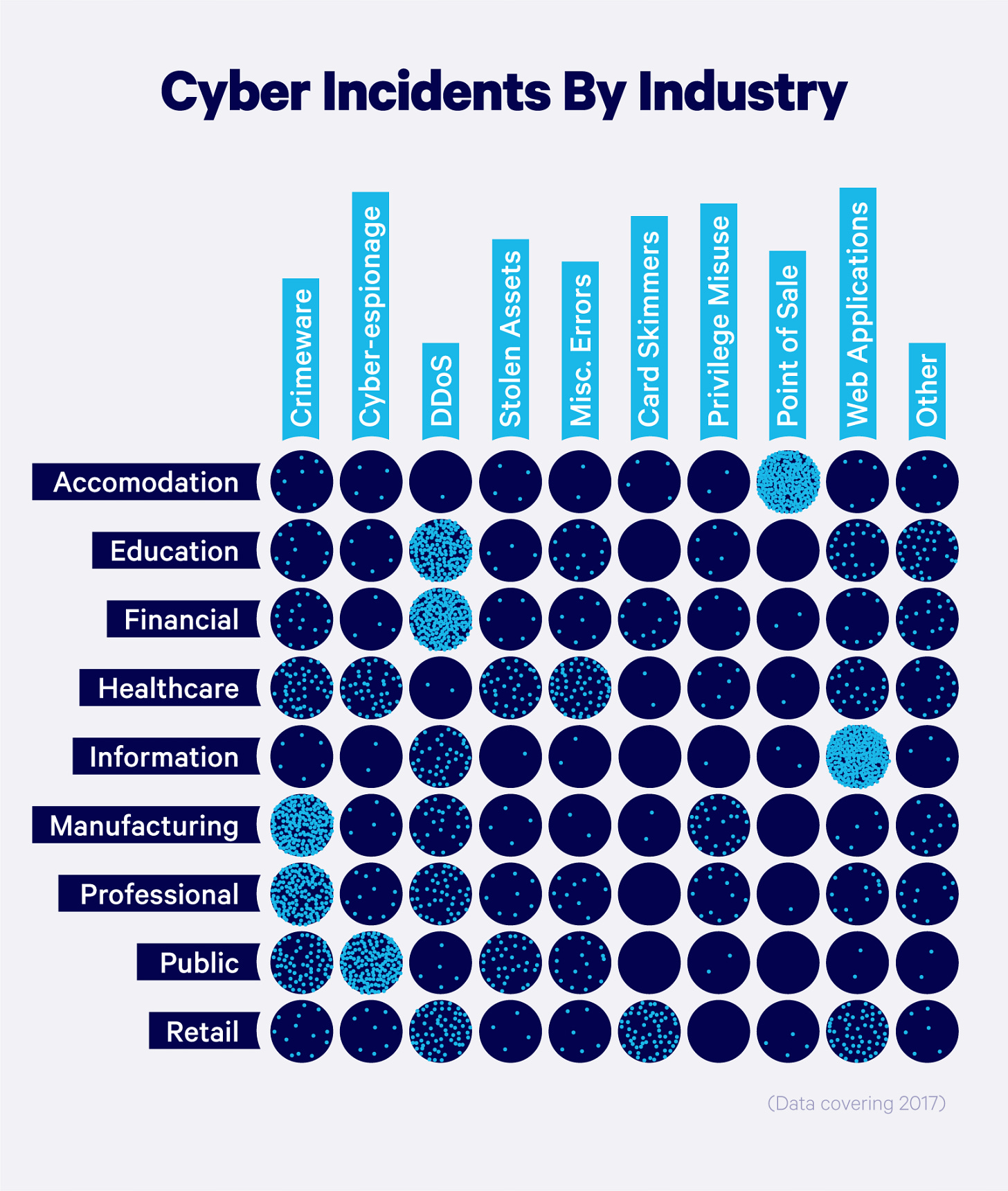
It’s likely your data has been involved in a leak already. In 2021, 50 million people were affected by T-Mobile’s data leak. Cybercriminals strike across every sector, using different attacks to get your information from anywhere they can. Healthcare is one of the most targeted sectors in the Stolen Assets and Cyber-espionage categories of attacks.
Review
Often, the company or provider will offer free credit monitoring, identity theft resolution services, and (usually) up to $1,000,000 of identity theft insurance. Sign-up! The letter informing you of the data leak will have a code to redeem this service.
Don’t wait, time is not on your side.
Seventy-three days passed from the day of the cyberattack to the date on the letter.
Check your settings
Assume that all account settings, of any service or provider, are privacy-unfriendly by default. Go through your settings and consider strict settings (not allowing GPS services, turning off access to photos, etc.).
Next, review the settings for your accounts and the information they have, especially the one that was just attacked. Restrict any settings that need to be and delete or replace any information that does not need to be there. (Cloaked fills in information to reroute it to you so that you’re never at risk of losing your real phone number. I recommend).
Thanks for reading and please forward to your friends… Reclaiming power starts with the awareness it needs to be fought for.